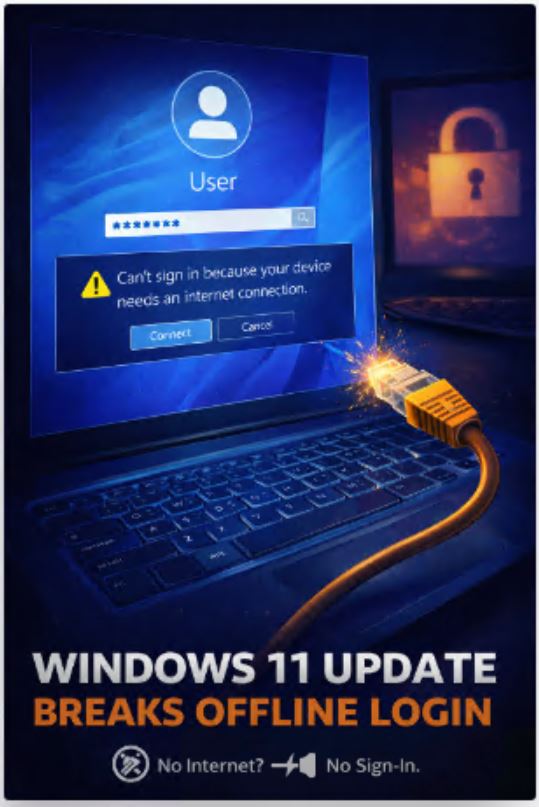
If you heard about a recent Windows 11 update causing “Can’t sign in because your device needs an internet connection” errors — you’re not imagining things. Multiple reports, official feedback and user reproduction steps confirm that after installing the latest cumulative update, some devices refuse to let users sign in if they cannot reach Microsoft’s servers. This isn’t a UI glitch. It’s a regression in authentication logic that has real operational impact — especially for enterprise environments with strict network controls or isolated endpoints.
Let’s unpack what’s happening, why it matters, and how to think about it from an IT and security perspective.
What triggers the issue
After applying the patch, a subset of Windows 11 devices starts blocking login attempts when:
• The device is domain-joined and cannot reach a domain controller.
• The device is not domain-joined and is using a Microsoft account, but cannot reach Azure AD.
• Network connectivity to authentication endpoints is filtered or blocked by firewalls, proxies or VPN split-tunnel settings.
Instead of falling back to cached credentials — which is how Windows has always worked — the system presents a message saying it requires an internet connection. In practical terms, users with no connectivity — or with connectivity only to internal networks — can be locked out of their machines.
This is not “Windows nags for updates.” This is a failure to authenticate locally when global authentication endpoints are unreachable.
Why cached logon exists
For decades, Windows has supported cached credentials:
• On domain-joined machines, if the DC is unreachable, Windows will use the last known good credentials to allow the user to log in.
• For Microsoft accounts, Windows caches a locally encrypted credential that lets you sign in even when offline.
Cached logon exists because environments are not always connected:
• Corporate VPNs that only allow specific traffic.
• Air-gapped facilities.
• Users working on planes or trains or in basements with flaky connectivity.
• Scenarios where DCs are reachable only through private networks.
Local authentication is a fundamental part of how Windows works. Breaking that — even accidentally — is a big deal.
The regressed behaviour
Post-update, affected devices are behaving as if:
• Cached credentials are disabled.
• The logon stack is refusing cached checks until it reaches out to an authentication endpoint.
• Timeout windows are short — so if Azure AD or the DC cannot respond quickly, the logon UWP returns the error.
This is not a “dialogue box surprise.” It’s a functional regression in the authentication flow.
Early reproduction by users shows:
- Power cycle laptop.
- Disable network (airplane mode / unplug ethernet / no Wi-Fi).
- Attempt login with a known local password (domain or Microsoft account).
- Windows refuses — says internet is required.
This indicates cached credential logic is being bypassed or short-circuited.
Who is most affected
This issue disproportionately impacts:
✔ Isolated users who connect only through VPN and have stringent egress filtering
✔ Domain-joined devices in networks where DCs are reachable only over internal routing
✔ Air-gapped endpoints (lab environments, OT networks)
✔ Users who rely on cached Microsoft account sign-in offline
✔ Rapid deployment scenarios where provisioning infrastructure is not yet connected to authentication endpoints
It is less visible for always-connected enterprise laptops with full internet access and direct Azure AD connectivity.
But for controlled networks where egress is limited, this behaviour breaks expected login patterns.
Why it’s a regression, not a feature
From a security perspective, Microsoft should validate credentials against authoritative sources when possible. But cached credentials exist for a reason: to allow access even when authoritative sources are unreachable.
Breaking cached logon means:
• Users can be completely locked out of their devices due to connectivity conditions.
• Helpdesk workloads spike because users can’t authenticate.
• VPN onboarding becomes a Catch-22 — no auth until VPN connects, no VPN until you log in.
This is not Zero Trust. This is Zero Access.
In tightly controlled networks, connectivity is always restricted by design. Authentication stacks must obey cached fallback logic. What is happening here seems to violate that principle.
What Microsoft has acknowledged
Microsoft has issued acknowledgements in response forums and support channels, indicating they are investigating. There are statements pointing to the update affecting cached credential logic and the logon UI incorrectly enforcing online checks.
However, there is no widespread official knowledge base article yet with root cause analysis or rollback recommendations.
This suggests the issue is not simply UI wording — it is internal state routing in the authentication stack.
Temporary mitigations
Until an official fix lands, organisations can consider:
1. Ensure network access to authentication endpoints from initial logon.
Allow traffic to domain controllers and Azure AD endpoints prior to login.
2. Adjust firewall and proxy policies to ensure the device can reach required endpoints — even before user sign-in.
3. Validate cached credential settings via Group Policy or MDM.
There may be registry or GPO flags to reinforce cached logon behaviour (such as Interactive logon: Number of previous logons to cache).
4. Avoid this patch in environments where offline logon is critical.
Block deployment via deployment rings until resolved.
These are not ideal. They are workarounds.
Broader implications
This incident underscores a difficult truth: modern authentication mechanics are becoming more tightly coupled to cloud connectivity even for basic local logic.
In pursuit of seamless SSO, token refresh and adaptive access policies, the authentication stack may be prioritising online checks at the expense of predictable offline fallback — and that is a dangerous trade-off in enterprise networks.
Consider these architectural realities:
• Domain controllers remain internal resources that may not be directly reachable by laptops until after VPN connects.
• Azure AD conditional access can require connectivity that doesn’t exist until after the logon UI completes authentication.
• Cached credentials are core to predictable logon behaviour in restricted networks.
Breaking any of these expectations undermines operational predictability.
Security vs predictability
There is a legitimate security motivation for verifying credentials against authoritative stores. But local authentication and cached logon exist precisely because wheels don’t always stay connected.
A robust authentication stack must:
✔ Validate against authoritative sources when reachable
✔ Fall back gracefully to cached credentials when they are not
✔ Avoid hard dependencies on external services for core functionality
✔ Respect network control policies and segmentation
If this regression reflects deeper changes in authentication logic, it may require architectural review of expected offline behaviours across Windows.
What we expect next
Microsoft will need to:
• Acknowledge the regression publicly
• Provide a KB with root cause, repro steps, and impact summary
• Offer a patch that restores correct fallback logic
• Clarify expected offline authentication behaviour going forward
For enterprise IT, this is not a “cosmetic UX fix.” It is a functional update that affects access control fundamentals.
Final thought
Local authentication — domain joined or Microsoft account — must continue to work even when offline. Cached credentials are not a workaround. They are core infrastructure behaviour.
When Windows undermines that, it doesn’t just frustrate users. It creates operational risk.
Enterprises with controlled networks, isolated endpoints, regulated environments and VPN remote access need predictable login behaviour. This issue turns that expectation on its head.
And until it is fixed, it remains an uncomfortable reminder that cloud integration cannot come at the expense of local authentication resilience.